Course TTb: The Engineering of Reliable Embedded Systems (on site)

Course TTb has a focus on the use of state-of-the-art ‘Time-Triggered‘ (TT) architectures to support the development of software for safe and reliable embedded systems.
Since 2014, we’ve delivered this popular 3-day course to more than 200 engineers in different parts of the world, with a class size of around 6 people being typical.
This page provides further information about delivery of Course TTb on your company site.
Course TTb is also available as a self-paced online training module.
[This page was last updated: 2020-12-18]
![]()
![]()
Who should take this course?
![]()
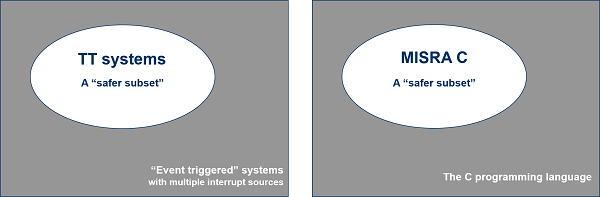
Course TTb covers the core techniques that are needed to design and implement TT software for use in safety-related embedded systems.
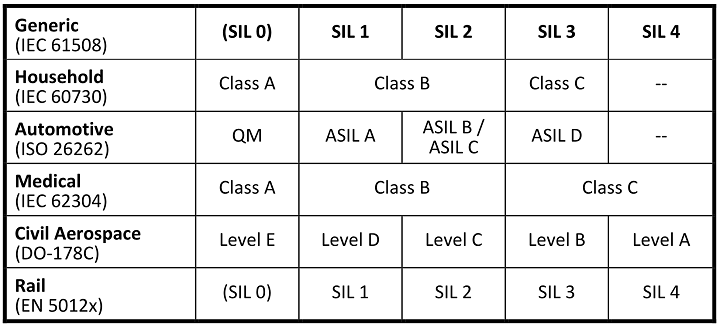
- Taking Course TTb will be of particular benefit to organisations that need to develop software for embedded systems in compliance with international safety standards, such as IEC 61508, ISO 26262, DO-178C, IEC 62304, ISO 13849, IEC 60335 and IEC 60730, up to ‘SIL 3’ / ‘ASIL D’ level or equivalent.
- Taking Course TTb will be of particular benefit to organisations that are ReliabiliTTy® licensees (or to organisations that are intending to become ReliabiliTTy licensees).
![]()
![]()
![]()
![]()
Pre-requisites
![]()
No knowledge of TT systems is assumed at the start of Course TTb, but you may find it helpful to read the introductory chapter in the ERES2 book before you attend: this material can be downloaded from the ERES2 page (free of charge).
Software examples discussed during the course are in the ‘C’ language. Some familiarity with this programming language is assumed throughout the course. If your C is very rusty, you might like to take a look at the ‘Embedded C‘ book before you attend TTb.
If you want to do further preparation, the videos for our TTa course are freely available.
![]()
![]()
Course dates and locations
![]()
The TTb course is delivered on your company site (anywhere in the world) on dates of your choosing.
![]()
![]()
Course structure
![]()
Course TTb is delivered in the form of 6 seminars over a period of three days.
The seminar material is supported by class discussions and group exercises.
![]()
![]()
Course contents
![]()
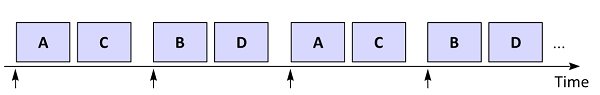
Course contents: Seminar 1 (Introduction)
The material in Seminar 1 provides a foundation for the remainder of the course. We start by considering some of the challenges involved in developing real-time systems, including the need to determine system response times and maximum CPU loading; we discuss task release jitter; we discuss ‘freedom from interference’ requirements. We consider the challenges involved in developing systems in compliance with international safety requirements such as ISO 26262 and IEC 61508. We consider the differences between time-triggered and event-triggered software architectures. We consider a simple implementation option for time-triggered co-operative (TTC) software architectures. We begin to consider how to design appropriate tasks for use with a TTC architecture. We consider some simple initial design examples.
Course contents: Seminar 2 (Task design for safe and reliable TT systems)
The TT systems considered in the TTb course typically consist of: [i] a set of tasks; [ii] a scheduler that will control the release of the tasks. A key goal of the techniques that are presented in this course is to enable developers to: [i] provide evidence of the circumstances in which it will be possible to detect interference between tasks, or between tasks and the scheduler (and vice versa), on a given processor; and [ii] provide evidence that the processor will – for example – be able to move into a ‘Fail-Safe Processor State’ or a ‘Limp-Home Processor Mode’ (as appropriate) in the event that such interference is detected. Achieving these goals requires that the tasks are designed and implemented correctly: we consider how this can be achieved in Seminar 2.
Course contents: Seminar 3 (Modes, States / Multiple processors)
In Seminar 3, we begin by considering systems with multiple operating modes. We discuss the importance of clear definitions. We provide definitions for ‘mode’ and ‘state’. We consider the challenge of ensuring safe transitions between modes. We discuss the use of (and design of) ‘same but different’ tasks for use in systems that require independence (including designs involving ‘ASIL decomposition’ and / or ‘backup tasks’). We then consider some of the challenges involved in creating distributed embedded systems: that is, TT systems involving multiple processors connected in some form of network using (for example) a bus or star topology. We consider both fully-synchronous designs and ‘Globally Synchronous, Locally Asynchronous’ (GALS) designs.
Course contents: Seminar 4 (Modelling TT systems)
In Seminar 4, we consider the modelling of TT systems. We consider the differences between synchronous and asynchronous task sets. We consider how to determine both the length of the major cycle, and the duration of the system initialisation phase. We demonstrate how to create a ‘Tick List’. We demonstrate how to use the Tick List to determine the response times, processor loading and task jitter. We demonstrate how ‘Worst Case Execution Time’ (WCET) and ‘Best Case Execution Time’ (BCET) measurements can be made effectively. We then turn our attention to schedulability analysis and scheduler configuration for TT designs with large task sets.
Course contents: Seminar 5 (Monitoring TT systems)
One key reason for choosing to use a TT software architecture is that the resulting system will have deterministic behaviour: we can therefore model key characteristics such as the maximum CPU load, the response time and levels of task jitter. Such models are necessarily based on various assumptions, including the following: we have operational peripherals on each processor; we can transfer data between tasks on the same processor without corruption; we can transfer data between processors without corruption. We explored techniques for testing these assumptions in Seminar 2 and Seminar 3. However, our models also assume that: all the processors in our system are operating correctly; we are running the correct processor software on each processor; we have an operational scheduler on each processor; all the tasks on each processor are operating correctly; we know the WCETs and BCETs of all tasks on each processor; we know the task execution sequence in each mode on each processor. If we fail to meet any of these assumptions at run time, our models may not be valid and we cannot be sure how the system will behave in the field. We therefore need to incorporate mechanisms in our system that will allow us to test these assumptions at run time, and we need to consider what we will do if the system does not pass one or more of these tests. Development of effective run-time monitoring components is a key part of the design process and – as a ‘rule of thumb’ – around 50% of the system software is likely to be devoted to such monitoring activities. We consider how to perform such run-time monitoring effectively in Seminar 5.

Course contents: Seminar 6 (Conventional RTOS vs. TT architecture in safety-related designs)
We begin Seminar 6 by exploring in more detail some of the challenges involved in designing and implementing systems in which more than one task must run simultaneously. We first review ways in which we can approximate multi-tasking systems using a single CPU and a conventional “real-time operating system” (RTOS). We consider rate-monotonic scheduling algorithms. We consider the use of mutexes and semaphores. We demonstrate the impact that priority inversion (PI) has on temporal determinism in all ET systems. We consider some partial solutions to PI problems through the use of “ceiling protocols”. We go on to consider TT designs that support task pre-emption, including both “hybrid” designs (TTH) and fully-pre-emptive designs (TTP). We revisit TTH and TTP designs and demonstrate how we can eliminate the problems of PI completely using TT architectures. We present a set of recommended ‘TT Platforms’ for use in reliable embedded systems (including those that must be developed in compliance with international safety standards, such as IEC 61508, ISO 26262 and DO-178). We explore ways in which we can employ a quasi-TT approach in designs that need to support additional (asynchronous) interrupts. We consider the use of ‘TT Wrappers’. We summarise the material presented throughout the course.
![]()
![]()
Trainer biodata

The on-site version of Course TTb is presented by Dr Michael J. Pont.
Michael was awarded a BSc degree (in Electronics and Electrical Engineering) by the University of Glasgow (UK) and a PhD (in Computer Science) by the University of Southampton (UK). He is the author of several successful books and more than 100 technical papers: he is named inventor / co-inventor on a number of patents. He has given invited presentations (including “keynote” and “plenary” talks) at a large number of international conferences.
Michael has been working in the field of time-triggered (TT) embedded systems for more than 20 years. He began this work in the academic sector, latterly as Professor of Embedded Systems Engineering at the University of Leicester (UK). During his time with the University of Leicester, Michael supervised more than 20 successful PhD projects.
Michael has helped numerous companies to create successful TT designs. Many of these designs have been produced in compliance with international safety standards and guidelines (including IEC 61508, ISO 26262 and DO-178).
Michael currently serves as Founder and CEO of SafeTTy Systems Ltd.
![]()
![]()
Course fee
![]()
The fee for delivery of the 3-day TTb course on your company site for up to 6 people is £6950.00*.
For larger groups (of 7 people or more), there is an additional fee of £500.00* for Person 7, Person 8 … up to a maximum of 24 people per course: for example, the cost of a 3-day course for 8 people is £7,950.00*.
The course fee includes:
- all training services;
- a printed copy of the course notes and a copy of the ‘ERES2’ book (paperback) for each participant.
*Quoted prices are in UK Pounds.
Course TTb discusses technology (‘ReliabiliTTy® Technology’) that is patented by SafeTTy Systems Ltd and is subject to copyright and other restrictions. Organisations registering for this course are expected to hold a ReliabiliTTy Technology Licence or to purchase a ReliabiliTTy Technology Evaluation Licence before the training begins.
Prices may be subject to UK VAT (depending on the location in which your training takes place). An additional charge will usually be made to cover travel and / or accommodation costs for the training team: any such charges will be agreed at the time of booking.
Formal quotations can be be provided.
![]()
![]()
Examination option

The on-site course option (detailed above) does not include the cost of taking the examinations on the SafeTTy Certified programme.
The typical fee for taking the exams is £2000* per group.
The examinations on the SafeTTy Certified programme (Level 2) operate as follows.
- approximately 2 months after the on-site course (after participants have had time to review and absorb the training material), our team will return to your site to conduct the formal written examination;
- these are ‘closed book’ exams, conducted under ‘university’ conditions;
- the exams are at approximately the same level as an advanced UK MSc course; the pass mark is 70%;
- signed and numbered certificates are awarded to candidates who are successful in the exams;
- some additional ‘staircase’ exercises will be provided after the intensive course, in order to help participants prepare for the exam; support is provided by e-mail over this period.
Please contact us for further information.
*Quoted prices are in UK Pounds. Prices may be subject to UK VAT (depending on the location in which your training takes place). An additional charge will usually be made to cover travel and / or accommodation costs for the training team: any such charges will be agreed at the time of booking. Formal quotations can be provided on request.
![]()
![]()
Further information
![]()
Please contact us if you have any questions about Course TTb.
![]()
![]()
